Nginx-https证书认证详解
Nginx-https
1.https基本概述
1.1.SSL主要功能
-
安全套接层
-
认证用户和服务器,确保数据发送到正确的客户机和服务器
-
加密数据以防止数据中途被窃取
-
维护数据的完整性,确保数据在传输过程中不被改变
HTTPS: 使用SSL来实现安全的通信
1.2.证书的概念
- 证书用于保证密钥的合法性
- 证书的主体可以是用户、计算机、服务等
- 证书格式遵循X.509标准
证书颁发流程
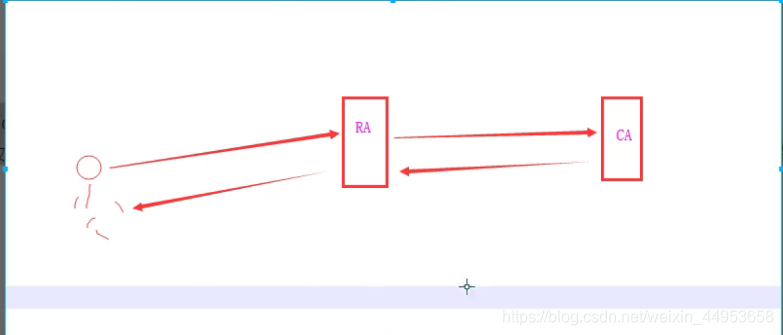
由运维人员将相关材料交给RA机构,再由RA机构将材料进行汇总交给CA机构,CA机构确认材料没有问题后,加紧证书交给RA机构,RA在交给运维人员
1.3.数字证书包含信息
- 使用者的公钥值
- 使用者标识信息(如名称和电子邮件)
- 有效期
- 颁发者表示信息
- 颁发者的数字签名
- 数字证书由权威公正的第三方机构即CA签发
1.4.PKI(公钥基础设施)
- 一对密钥(私钥和公钥)
- 公钥即所有人都可以获取而私钥只有个人可以用于,公钥也可以相当于一把锁子,而私钥相当于一把钥匙
- 公钥加密,私钥解密,这是数据加密的原理
- 私钥加密,公钥解密,这是数字签名的原理
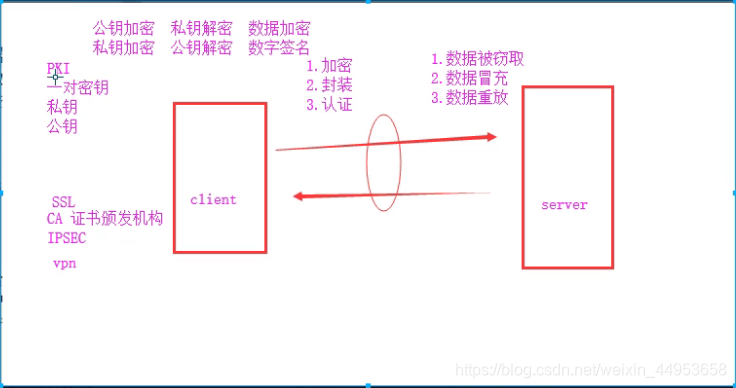
1.5.PKI的作用
- 保密性:如何保证电子商户中涉及的大量保密信息在公开网络的传输过程中不被窃取;
- 完整性:如何保证电子商务中所传输的交易信息不被中途篡改及通过重复发送进行虚假交易(如我在银行取了一百万,结果跟银行说我没有取又想重新取一遍)
- 身份认证与授权:在电子商务的交易过程中,如何对双方进行认证,以保证交易双方身份的正确性
- 抗抵赖:在电子商务的交易完成后,如何保证交易的任何一方无法否认已发生的交易(如小明给小红发了一个电子邮件,其中小黄窃取了邮件内容,并进行篡改,再发送给小红,结果做了数字签名,小黄即使不承认也能有证据证明确实是他窃取了数据)
1.6.HTTPS证书的选择
- 专业版OV型证书,不显示企业名称
- 高级版EV型证书,显示企业名称
1.7.HTTPS证书购买选择
- 保护一个域名www
- 保护五个域名www images cdn test m
- 通配符域名*.know.com
- 一个正式只能为一个域名提供https
1.8.HTTPS注意事项
- Https不支持三级域名解析
- Https不支持续费,证书到期需要重新申请进行替换
- Https显示绿色,说明整个网站的URL都是https的
- Https显示黄色,因为网站代码中包含http的不安全连接
- Https显示红色,证书是假的或过期了
2.https证书申请
2.1.配置苹果要求的证书
- 服务器所有连接使用TLS1.2版本以上
- HTTPS证书必须使用SHA246以上哈希算法前面
- HTTPS证书必须使用RSA 2048位或ECC256位以上公钥算法
- 使用前项加密技术
2.2.密钥生成操作步骤
- 生成key密钥
- 生成证书签名请求文件
- 生成证书签名文件
2.3.申请证书文件
1.检查当前环境
[root@localhost nginx]# openssl version
OpenSSL 1.0.2k-fips 26 Jan 2017
2.检查nginx是否有ssl模块
[root@localhost nginx]# nginx -V
--with-http_ssl_module
3.创建证书存放目录
[root@jxl ~]# mkdir -p /etc/nginx/ssl_key
[root@jxl ~]# cd /etc/nginx/ssl_key
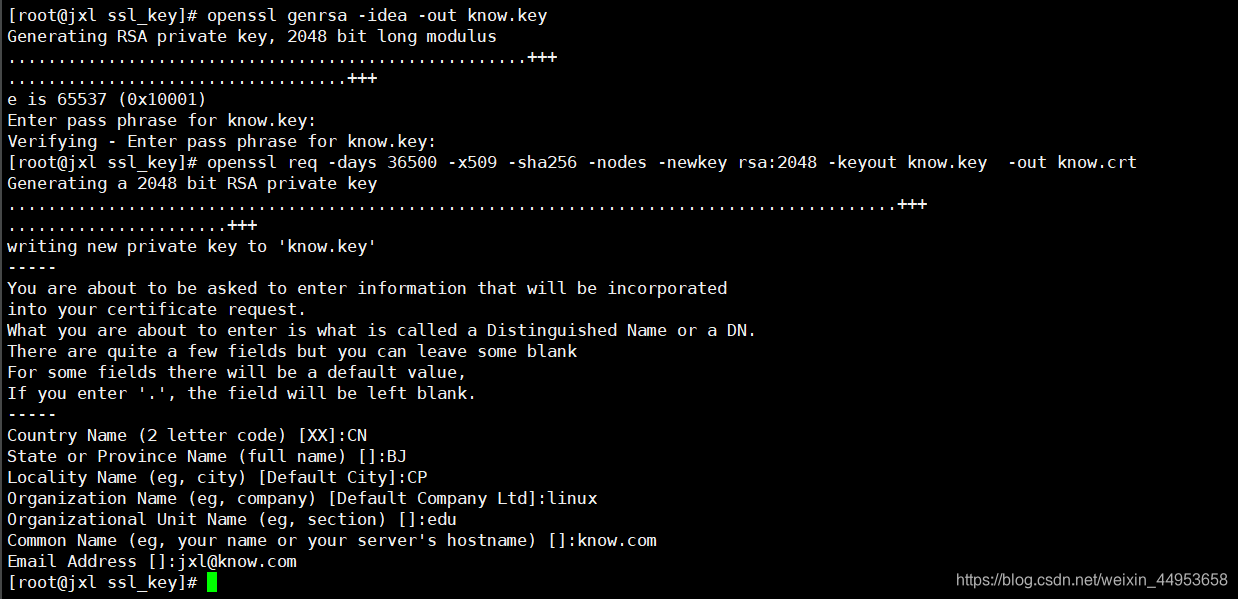
4.使用openssl充当CA权威机构创建私钥,生产环境不能使用此方式生成证书,不被互联网CA认可
[root@localhost ssl_key]# openssl genrsa -idea -out know.key 2048
Generating RSA private key, 2048 bit long modulus
.................................................+++
.........+++
e is 65537 (0x10001)
Enter pass phrase for know.key: //输入认证密码
Verifying - Enter pass phrase for know.key: //再次输入密码
5.生成自签证书,同时去掉私钥密码
[root@jxl ssl_key]# openssl req -days 36500 -x509 -sha256 -nodes -newkey rsa:2048 -keyout know.key -out know.crt
Generating a 2048 bit RSA private key
.........................................................................................+++
......................+++
writing new private key to 'know.key'
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN //国家
State or Province Name (full name) []:BJ //州
Locality Name (eg, city) [Default City]:CP //城市
Organization Name (eg, company) [Default Company Ltd]:linux //单位
Organizational Unit Name (eg, section) []:edu //主机名
Common Name (eg, your name or your server's hostname) []:know.com //域名
Email Address []:jxl@know.com //邮箱
参数详解
req 用于创建新证书
newkey 表示创建的是新证书
x509 表示定义证书的格式是标准格式
keyout 表示调用的私钥文件信息
out 表示输出证书文件信息
days 表示证书的有效期
3.https具体配置
3.1.https配置语法
开启ssl
语法:ssl on|off;
默认:ssl off;
配置区域:http,server
指定证书文件路径
语法:ssl_certificate file;
默认:-
配置区域:http,server
指定私钥key文件路径
语法:ssl_certificate_key file;
默认:-
配置区域:http,server
3.2.https配置
1.编辑站点配置文件
[root@localhost conf.d]# vim https_know.conf
#https_know
server {
listen 443;
server_name edu.know.com;
ssl on;
ssl_certificate ssl_key/know.crt;
ssl_certificate_key ssl_key/know.key;
location / {
root /web;
index index.html;
}
}
2.注意事项,如果在检测语法提示如下内容,不过也不影响使用
nginx: [warn] the "ssl" directive is deprecated, use the "listen ... ssl" directive instead in /etc/nginx/conf.d/https_know.conf:4
处理方法:
编辑配置文件将ssl on一行删除,修改listen一行为listen 443 ssl;
3.重载服务
[root@localhost conf.d]# nginx -t
[root@localhost conf.d]# systemctl reload nginx
3.3.https跳转1
通过访问http://edu.know.com跳转至https://edu.know.com
实现思路:
由于http是默认监听80端口,因此我们在定义一个server用来监听80端口,然后定义一个rewrite即可
实现方式1.
server {
listen 443 ssl;
server_name edu.know.com;
ssl_certificate ssl_key/know.crt;
ssl_certificate_key ssl_key/know.key;
location / {
root /web/know;
index index.html;
}
}
server {
listen 80;
server_name edu.know.com;
rewrite .* https://edu.know.com;
}
方式2
rewrite .* https://$server_name$request_uri;
方式3
rewrite .* https://$host$request_uri;
方式4
rewrite (.*) https://$server_name$1;

3.4.https跳转2
当访问know.com时跳转至https://edu.know.com
实现思路:定义一个server,server_name为know.com然后定义rewrite
[root@localhost conf.d]# vim https_know.conf
server {
listen 443 ssl;
server_name edu.know.com;
#ssl on;
ssl_certificate ssl_key/know.crt;
ssl_certificate_key ssl_key/know.key;
location / {
root /web/know;
index index.html;
}
}
server {
listen 80;
server_name know.com;
rewrite (.*) https://edu.know.com;
}

4.多站点https配置
4.1.申请所有站点证书
1.shangmei.com
[root@localhost ~]# cd /etc/nginx/ssl_key/
[root@localhost ssl_key]# openssl genrsa -idea -out shangmei.key
[root@localhost ssl_key]# openssl req -days 36500 -x509 -sha256 -nodes -newkey rsa:2048 -keyout shangmei.key -out shangmei.crt
2.know.com
[root@localhost ~]# cd /etc/nginx/ssl_key/
[root@localhost ssl_key]# openssl genrsa -idea -out know.key
[root@localhost ssl_key]# openssl req -days 36500 -x509 -sha256 -nodes -newkey rsa:2048 -keyout know.key -out know.crt
4.2.配置站点文件
1.shangmei.com
[root@localhost conf.d]# cat https_shangmei.conf
#shangmei.com
server {
listen 443 ssl;
server_name gw.shangmei.com;
ssl_certificate ssl_key/shangmei.crt;
ssl_certificate_key ssl_key/shangmei.key;
location / {
root /web/shangmei;
index index.html;
}
}
[root@localhost conf.d]# cat https_know.conf
#https_know
server {
listen 443 ssl;
server_name edu.know.com;
#ssl on;
ssl_certificate ssl_key/know.crt;
ssl_certificate_key ssl_key/know.key;
location / {
root /web/know;
index index.html;
}
}
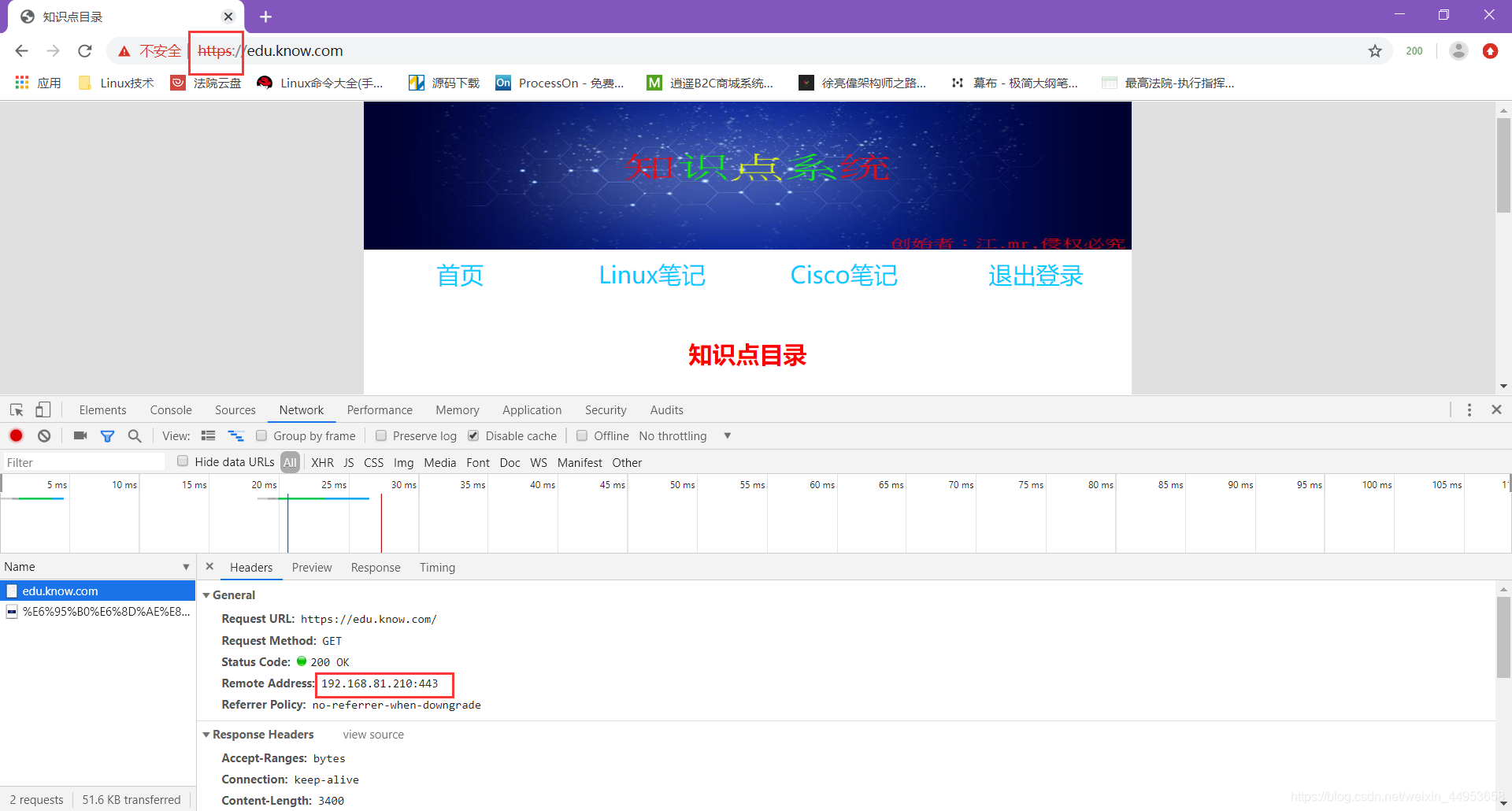
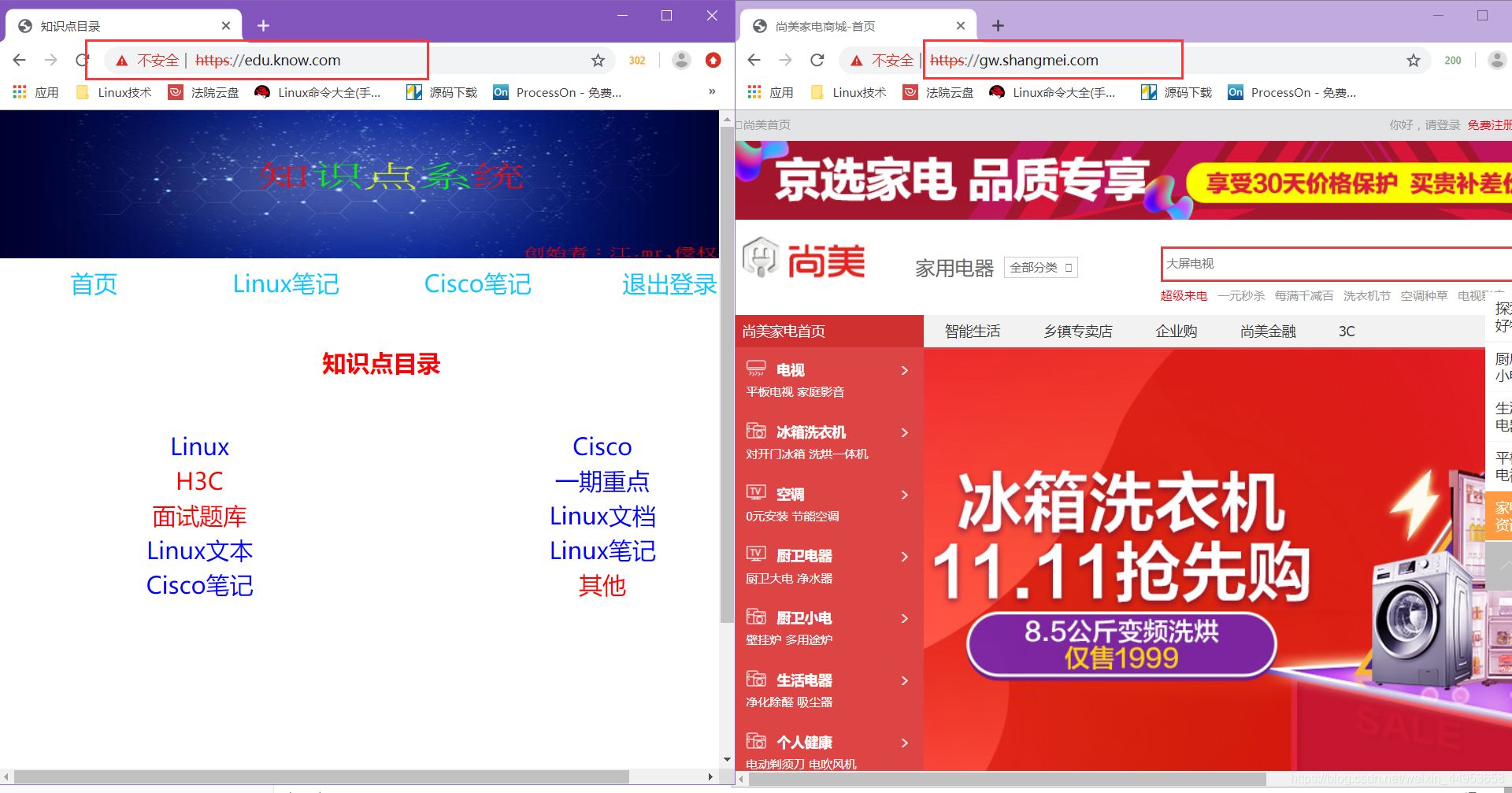
页面访问
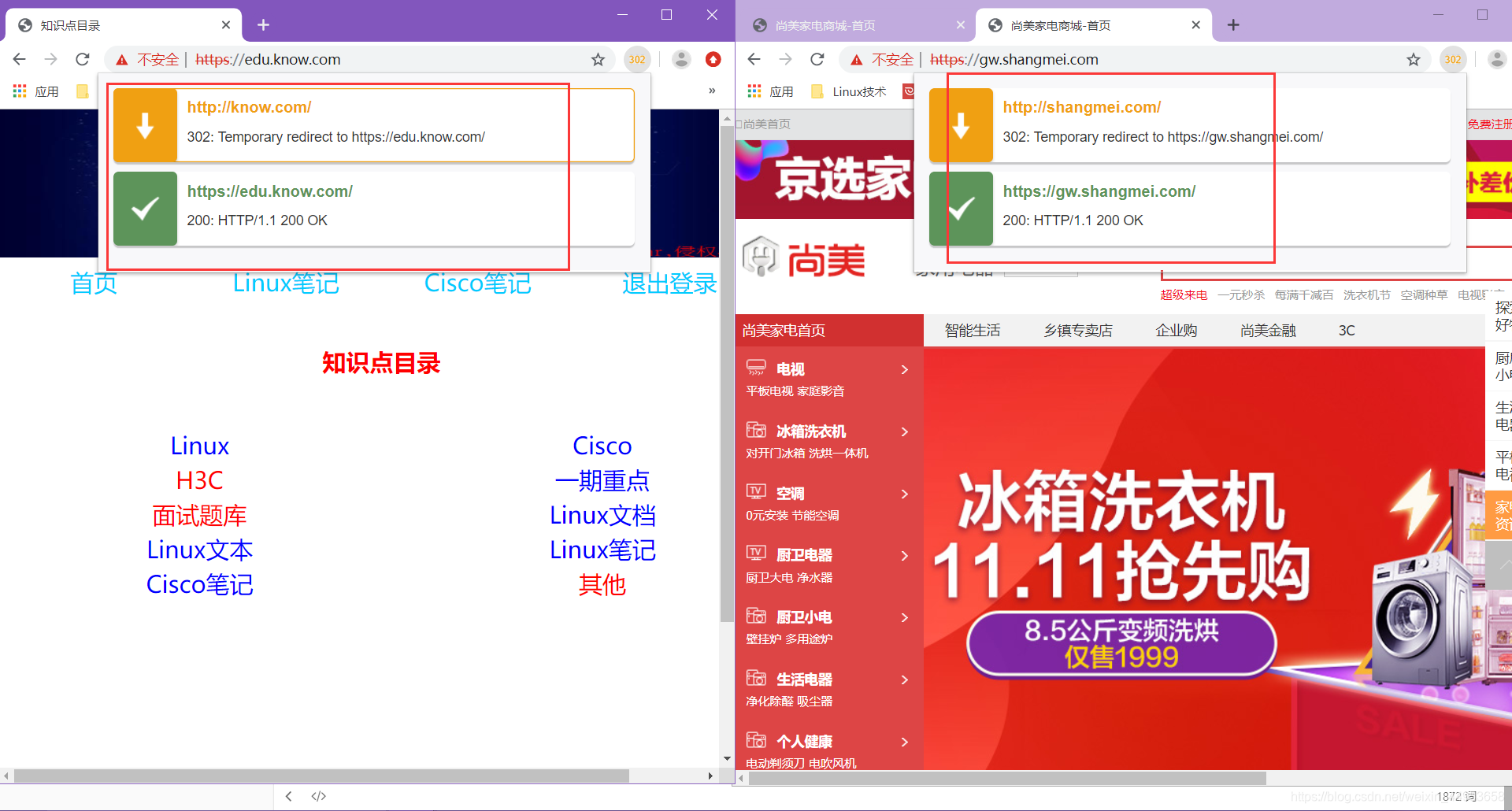
4.4.配置rewrite
访问二级域名即可跳转至对应页面
shangmei.com
[root@localhost conf.d]# cat https_shangmei.conf
#shangmei.com
server {
listen 443 ssl;
server_name gw.shangmei.com;
ssl_certificate ssl_key/shangmei.crt;
ssl_certificate_key ssl_key/shangmei.key;
location / {
root /web/shangmei;
index index.html;
}
}
server {
listen 80;
server_name shangmei.com;
rewrite (.*) https://gw.shangmei.com$1;
}
know.com
[root@localhost conf.d]# cat https_know.conf
#https_know
server {
listen 443 ssl;
server_name edu.know.com;
#ssl on;
ssl_certificate ssl_key/know.crt;
ssl_certificate_key ssl_key/know.key;
location / {
root /web/know;
index index.html;
}
}
server {
listen 80;
server_name know.com;
rewrite (.*) https://edu.know.com;
}
5.负载均衡https跳转配置
5.1.环境配置
| 角色 | ip |
|---|---|
| nginx负载 | 192.168.81.210 |
| web01 | 192.168.81.220 |
| web03 | 192.168.81.230 |
5.2.配置web节点
web01
[root@jxl conf.d]# vim https_know.conf
#https_know
server {
listen 80;
server_name edu.know.com;
#ssl on;
#ssl_certificate ssl_key/know.crt;
#ssl_certificate_key ssl_key/know.key;
location / {
root /web/know;
index index.html;
}
}
web02
[root@localhost conf.d]# vim https_know.conf
#https_know
server {
listen 80;
server_name edu.know.com;
root /web/know;
index index.html;
}
节点测试
[root@localhost conf.d]# echo "127.0.0.1 edu.know.com" > /etc/hosts
[root@localhost conf.d]# curl edu.know.com | less
5.3.配置nginx负载均衡+https
1.开启rewrite日志
[root@localhost conf.d]# vim ../nginx.conf
http {
.....
error_log /var/log/nginx/error.log notice;
rewrite_log on;
.....
}
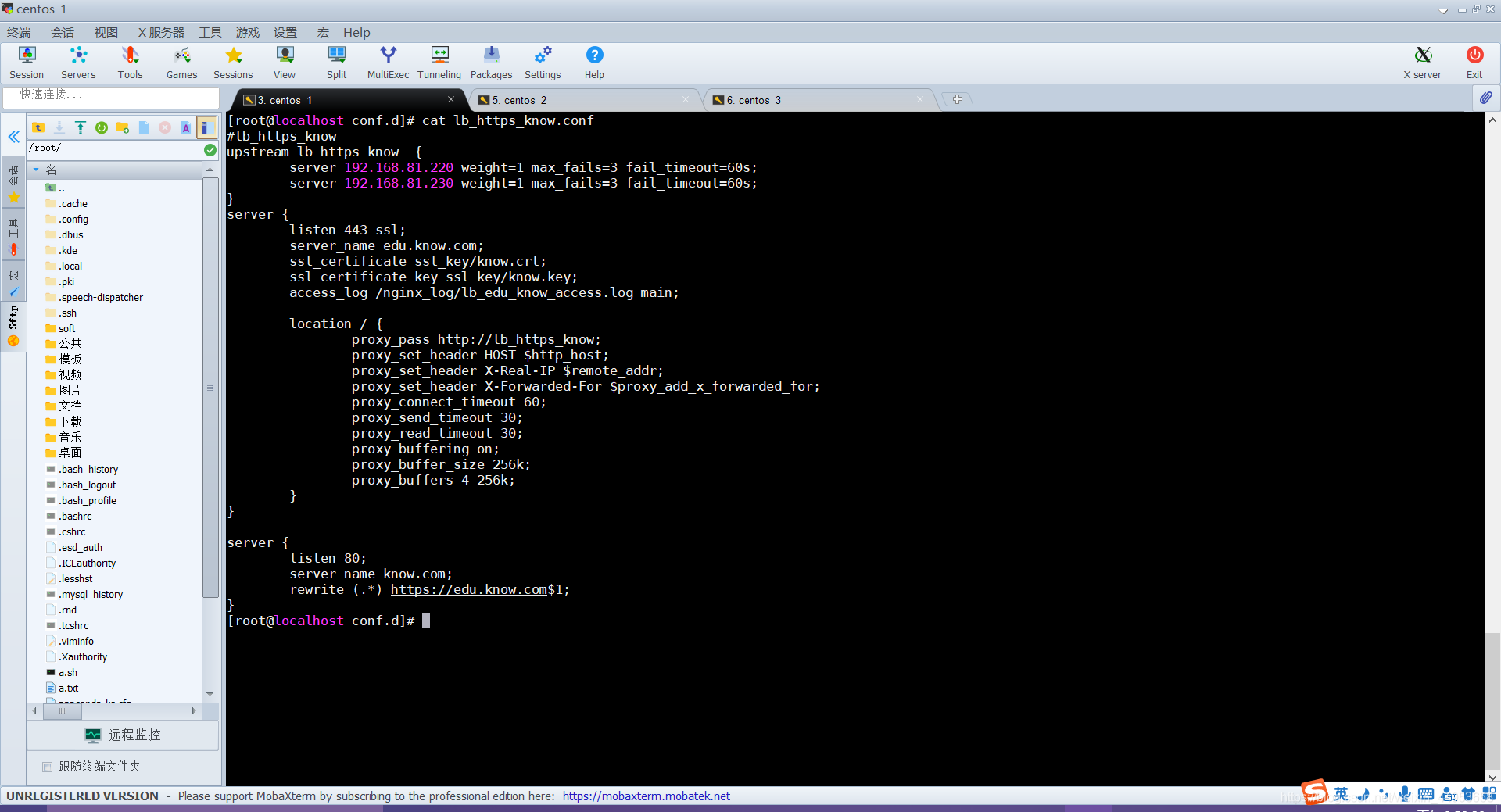
2.配置负载均衡
[root@localhost conf.d]# vim lb_https_know.conf
#lb_https_know
upstream lb_https_know {
server 192.168.81.220 weight=1 max_fails=3 fail_timeout=60s;
server 192.168.81.230 weight=1 max_fails=3 fail_timeout=60s;
}
server {
listen 443 ssl;
server_name edu.know.com;
ssl_certificate ssl_key/know.crt;
ssl_certificate_key ssl_key/know.key;
access_log /nginx_log/lb_edu_know_access.log main;
location / {
proxy_pass http://lb_https_know;
proxy_set_header HOST $http_host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_connect_timeout 60;
proxy_send_timeout 30;
proxy_read_timeout 30;
proxy_buffering on;
proxy_buffer_size 256k;
proxy_buffers 4 256k;
}
}
5.4.配置rewrite跳转
[root@localhost conf.d]# vim lb_https_know.conf
server {
listen 80;
server_name know.com;
rewrite (.*) https://edu.know.com$1;
}
配置文件最终配置
访问效果

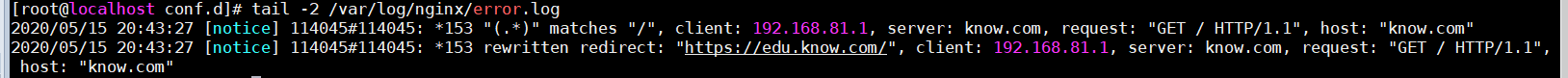
5.5.日志效果
访问日志
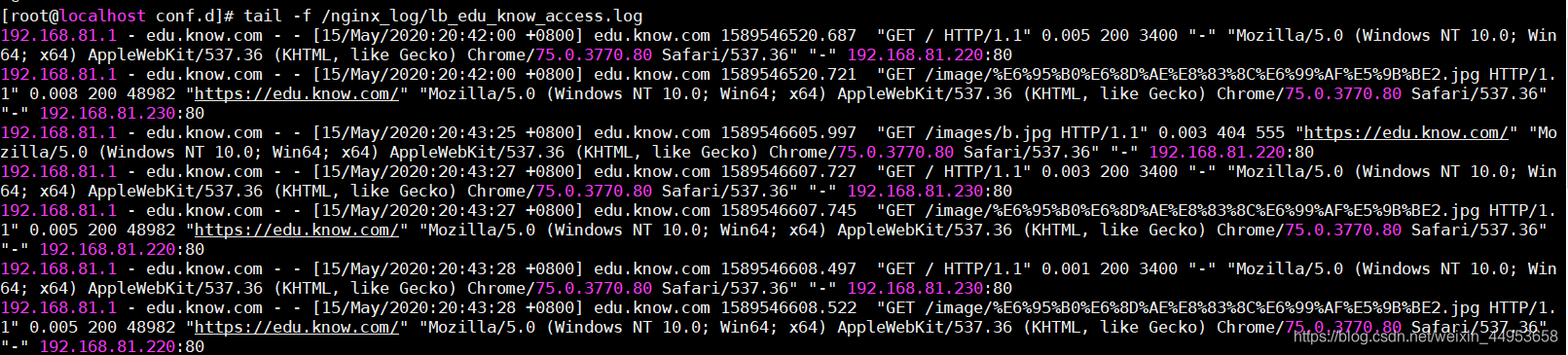
错误日志—记录rewrite跳转
6.总结
PKI
公钥基础设施
证书
加密算法
SSL
安全套接层
HTTPS
通过SSL传输数据
可以这样来说明这个原理:http和ssl结合升级为https,通过ssl加密传输数据,ssl是pki实现的一种方式,pki可以生成证书、加密算法,有两种算法:公加私解—数据加密,私家公解—数字签名
证书申请其实和身份证颁发的流程是一样的,首先由运维人员将相关材料交给RA机构,再由RA机构将材料进行汇总交给CA机构,CA机构确认材料没有问题后,加紧证书交给RA机构,RA在交给运维人员,而身份证颁发则是个人将自己的身份信息交给公安局,公安局在交给办证的机构,机构将身份证做完后发给公安局,公安局通知个人来取。
目录 返回
首页