Docker 为你的镜像仓库Harbor部署HTTPS
Harbor 部署HTTPS
生成SSL证书
配置https必须要有ssl证书,ssl证书可以是受信任的第三方CA签发的,大部分是花钱要买的,要域名证书公司帮你签发。这些都是受信任的,大概一个域名3000左右。
当然你也可以使用自签证书,比如使用openssl生成证书,或者使用cfssl工具去生成证书。
我这里使用自签证书,创建生成证书的目录ssl,并且下载配置cfssl工具
[root@reg harbor]# mkdir /ssl
[root@reg harbor]# cd /ssl/
#这个脚本主要是下载cfssl这个工具。然后二进制文件放在系统二进制目录下面
[root@localhost ssl]# cat cfssl.sh
wget https://pkg.cfssl.org/R1.2/cfssl_linux-amd64
wget https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64
wget https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64
chmod +x cfssl*
mv cfssl_linux-amd64 /usr/bin/cfssl
mv cfssljson_linux-amd64 /usr/bin/cfssljson
mv cfssl-certinfo_linux-amd64 /usr/bin/cfssl-certinfo
[root@localhost ssl]# chmod o+x cfssl.sh
[root@localhost ssl]# bash cfssl.sh
[root@reg ssl]# cfssl 可以看到直接可以使用了,有了这个工具之后就可以基于这个工具生成证书
cfssl cfssl-certinfo cfssljson
cfssl cfssljson 这两个工具配合的使用 cfssl-certinfo 查看证书的工具首先创建CA,你花钱购买的证书也是CA。所以自签也需要CA,CA就是证书颁发机构,这个必须得有。先创建CA的两个json文件,cfssl工具就通过json的配置文件来生成证书CA的。
cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"kubernetes": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF
cat > ca-csr.json <<EOF
{
"CN": "kubernetes",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
EOF使用cfssl工具生成初始化CA
[root@localhost ssl]# ls
ca-config.json ca-csr.json cfssl.sh
[root@localhost ssl]# cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
2020/11/13 19:56:15 [INFO] generating a new CA key and certificate from CSR
2020/11/13 19:56:15 [INFO] generate received request
2020/11/13 19:56:15 [INFO] received CSR
2020/11/13 19:56:15 [INFO] generating key: rsa-2048
2020/11/13 19:56:16 [INFO] encoded CSR
2020/11/13 19:56:16 [INFO] signed certificate with serial number 475903264239659842602085673089005502135504585581
[root@localhost ssl]# ls
ca-config.json ca.csr ca-csr.json ca-key.pem ca.pem cfssl.sh
ca-key.pem ca.pem
这两个是CA相关的证书,通过这个CA来签署服务端证书先创建服务端证书的请求文件,请求文件里面CN是域名,也就是你现在使用什么域名就写什么域名
cat > reg.harbor.com-csr.json <<EOF
{
"CN": "reg.harbor.com",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}
EOF使用这个配置文件生成一个域名证书,这个域名要和docker harbor的域名保持一致
[root@localhost ssl]# cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes reg.harbor.com-csr.json | cfssljson -bare reg.harbor.com
2020/11/13 20:00:32 [INFO] generate received request
2020/11/13 20:00:32 [INFO] received CSR
2020/11/13 20:00:32 [INFO] generating key: rsa-2048
2020/11/13 20:00:33 [INFO] encoded CSR
2020/11/13 20:00:33 [INFO] signed certificate with serial number 259717222341344224885262503583243473042738884138
2020/11/13 20:00:33 [WARNING] This certificate lacks a "hosts" field. This makes it unsuitable for
websites. For more information see the Baseline Requirements for the Issuance and Management
of Publicly-Trusted Certificates, v.1.1.6, from the CA/Browser Forum (https://cabforum.org);
specifically, section 10.2.3 ("Information Requirements").生成好之后会为reg.harbor.com域名颁发两个证书,一个是私钥 reg.harbor.com-key.pem,另外一个是数字证书reg.harbor.com.pem
[root@localhost ssl]# ls
ca-config.json ca-csr.json ca.pem reg.harbor.com.csr reg.harbor.com-key.pem
ca.csr ca-key.pem cfssl.sh reg.harbor.com-csr.json reg.harbor.com.pemHarbor启用HTTPS
修改harbor的配置文件harbor.yml
[root@reg harbor]# vim harbor.yml
https:
port: 443
指定刚刚生成证书的路径
certificate: /ssl/reg.harbor.com.pem
private_key: /ssl/reg.harbor.com-key.pem
重新生成配置文件
[root@reg harbor]# ./prepare 重新生成配置文件,将证书写进去重建容器证书才会生效,down先帮你停止容器然后再删除容器

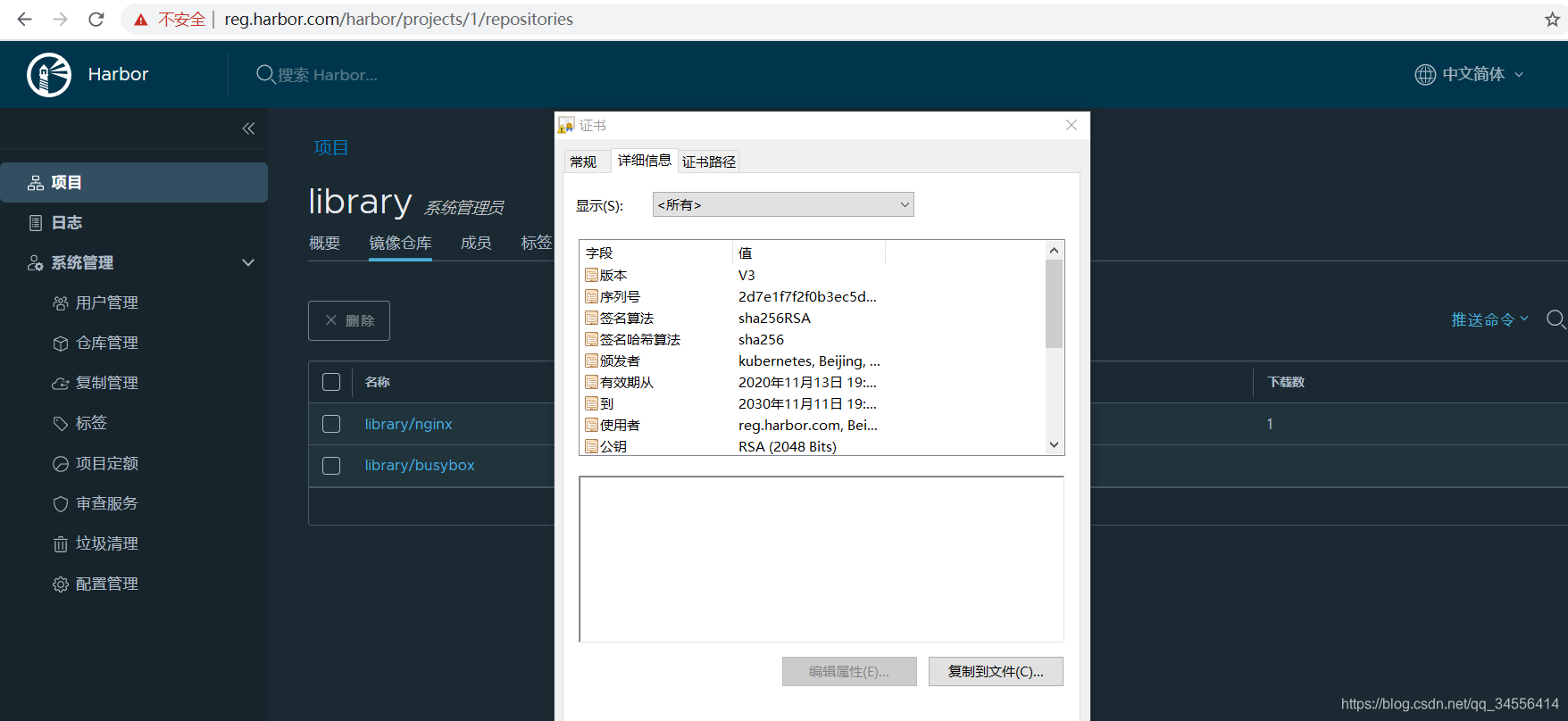
现在就实现了通过https访问仓库了
将数字证书复制到Docker主机
docker仓库部署好之后,我们需要做的是在其它节点连接自己的仓库,经常会出现“x509 certificate signed by unknown authority.”错误。下面如何解决自建仓库出现x509错误的方法
[root@localhost ~]# docker login reg.harbor.com
Username: admin
Password:
Error response from daemon: Get https://reg.harbor.com/v2/: x509: certificate has expired or is not yet valid要让docker访问的时候携带数字证书,完成正常的http握手,校验
这样要将之前的数字证书拷贝到docker主机,因为校验主要是去证书是否可信任或者有没有过去(由于是自签名证书,默认是不受Docker信任的,故而需要将证书添加到Docker的根证书中,Docker在CentOS 7中,证书存放路径是/etc/docker/certs.d/域名.crt)
192.168.179.99是一台docker主机,即要拉取镜像的主机
[root@reg ssl]# scp reg.harbor.com.pem root@192.168.179.99:~在docker主机上执行
[root@localhost reg.harbor.com]# mkdir /etc/docker/certs.d/reg.harbor.com -p
[root@localhost ~]# ls
anaconda-ks.cfg reg.harbor.com.pem
[root@localhost ~]# cp reg.harbor.com.pem /etc/docker/certs.d/reg.harbor.com/reg.harbor.com.crt
[root@localhost ~]# docker login reg.harbor.com
Username: admin
Password:
WARNING! Your password will be stored unencrypted in /root/.docker/config.json.
Configure a credential helper to remove this warning. See
https://docs.docker.com/engine/reference/commandline/login/#credentials-store
Login Succeeded
脚本实现
cfssl工具脚本
[root@localhost ssl]# cat cfssl.sh
wget https://pkg.cfssl.org/R1.2/cfssl_linux-amd64
wget https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64
wget https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64
chmod +x cfssl*
mv cfssl_linux-amd64 /usr/bin/cfssl
mv cfssljson_linux-amd64 /usr/bin/cfssljson
mv cfssl-certinfo_linux-amd64 /usr/bin/cfssl-certinfo生成证书脚本
[root@localhost ssl]# cat certs.sh
cat > ca-config.json <<EOF
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"kubernetes": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF
cat > ca-csr.json <<EOF
{
"CN": "kubernetes",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
EOF
cfssl gencert -initca ca-csr.json | cfssljson -bare ca -
cat > reg.harbor.com-csr.json <<EOF
{
"CN": "reg.harbor.com",
"hosts": [],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}
EOF
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=kubernetes reg.harbor.com-csr.json | cfssljson -bare reg.harbor.com
目录 返回
首页